Linux Malware Incident Response: A Practitioner's Guide to Forensic Collection and Examination of Volatile Data: An Excerpt from Malware Forensic Field Guide for Linux Systems: Malin, Cameron H., Casey BS MA, Eoghan,
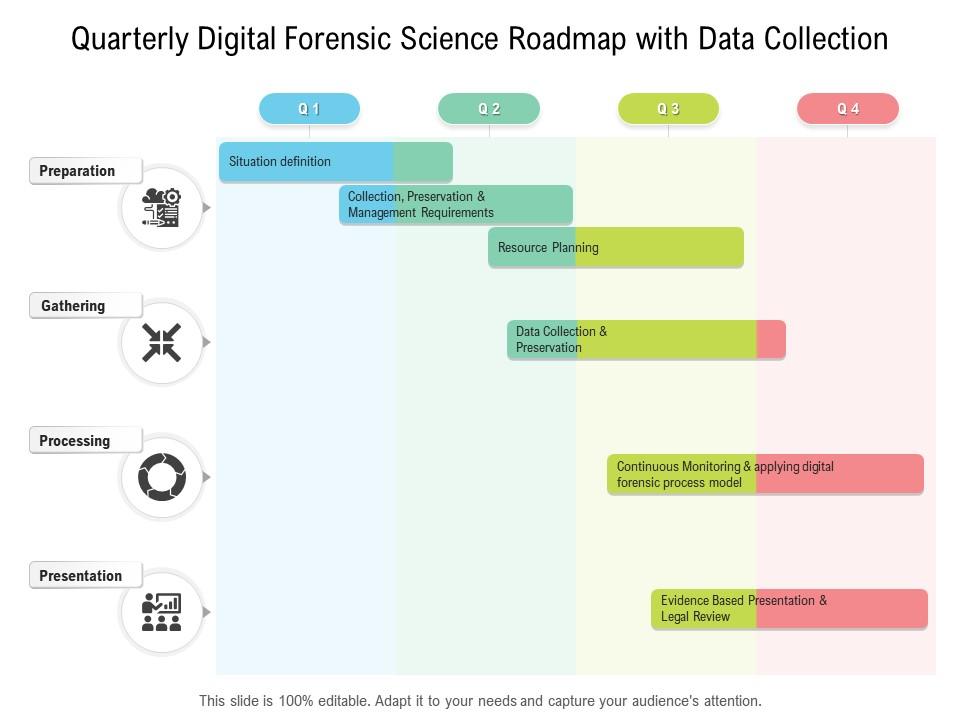
Quarterly Digital Forensic Science Roadmap With Data Collection | PowerPoint Slides Diagrams | Themes for PPT | Presentations Graphic Ideas

Applied Sciences | Free Full-Text | Methodology for Forensics Data Reconstruction on Mobile Devices with Android Operating System Applying In-System Programming and Combination Firmware
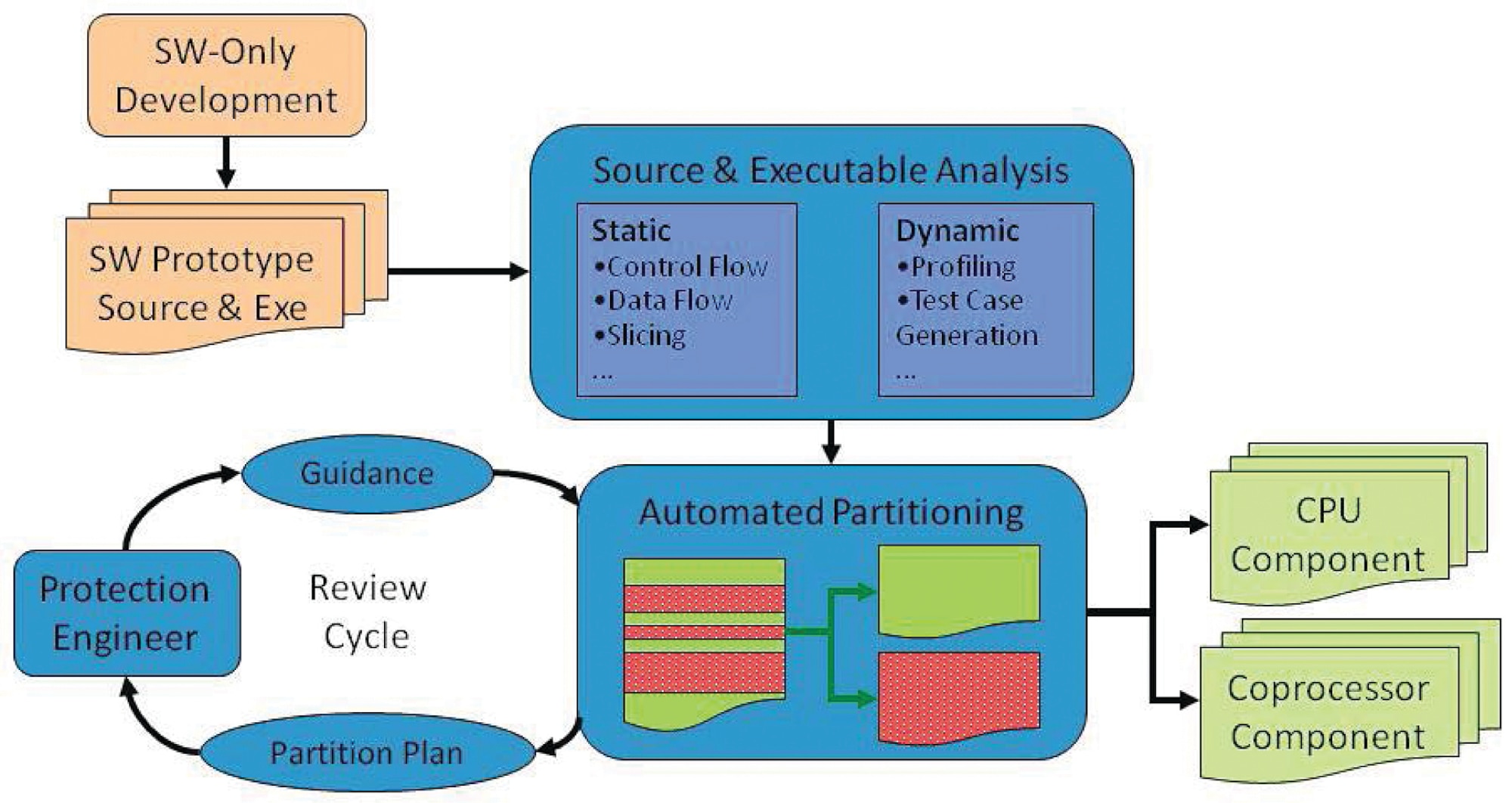
Software Protection to Deter Malicious Forensic Data Collection and Exploitation > Wright-Patterson AFB > Article Display

Secrets of Effective Cyber Forensics Investigation and Data Collection | Reserve Bank Information Technology Private Limited (ReBIT)

Forensic Data Collections 2.0: The Guide for Defensible & Efficient Processes: Fried, Robert B: 9781636835006: Amazon.com: Books

ediligence | Forensic Data Collection in Latin America: Behind the Scenes with a Government Investigator in Colombia